(Medium) Blind SSRF in SPIP 4.4.8 Syndication Feature and stored XSS
CVE-2026-27472 (CVSS-B 5.3 MEDIUM)
I found a blind SSRF vulnerability within SPIP (a well-known french CMS) that can be triggered by an authenticated administrator via the url_syndic field in the back-office. It allows an attacker to blindly map the internal network.
MITRE link here.
Blog post from SPIP here.
Details
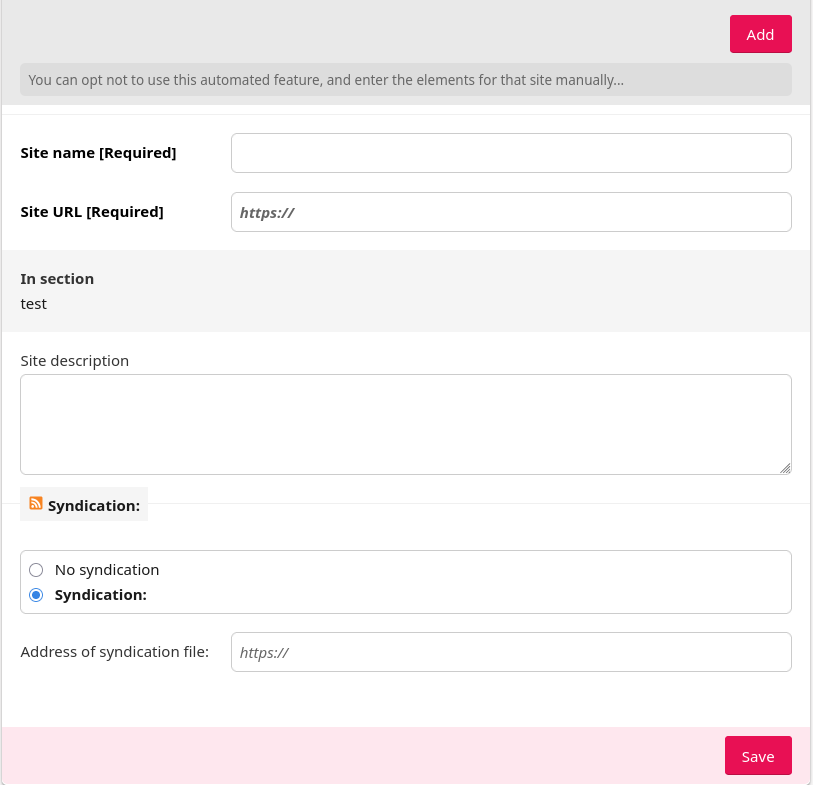
When referencing a site, there is a Syndication field which the application does not validates at all. It accepts the tcp:// wrapper and does not filter private IPs.
Vulnerable code (plugins-dist/sites/syndic/atomrss.php):
function syndic_atomrss_dist($url_syndic) {
// Aller chercher les donnees du RSS et les analyser
include_spip('inc/distant');
$res = recuperer_url($url_syndic, ['transcoder' => true]);
if (
!$res
or !$res['page']
or intval($res['status'] / 100) != 2
) {
$items = _T('sites:avis_echec_syndication_02');
} else {
$items = analyser_backend($res['page'], $url_syndic);
}
return $items;
}
As you can see, there are no filters on the user controlled field url_syndic which is passed to recuperer_url(). recuperer_url simply does a request on the given URL and does not check for a specific protocol or IP.
PoC
-
Log in as an administrator.
-
Make sure that in the
Site contentconfiguration,Sites referencing and syndicationis onManage website directory. -
Navigate to a section and click
Reference a site. -
In the
Syndicationfield, clickSyndicationand enter a target IP and port:tcp://127.0.0.1:22. -
Save.
-
Compare the response time against a an open port (
tcp://127.0.0.1:80). You can also click onUpdate nowon the page of the syndicated site to trigger the SSRF.
Note
On the same field, you can also trigger a stored XSS by inputing javascript:alert(1) instead. Then by clicking the RSS icon on the syndicated site page (?exec=site&id_syndic=1), you will trigger the alert. This is CVE-2026-27474.